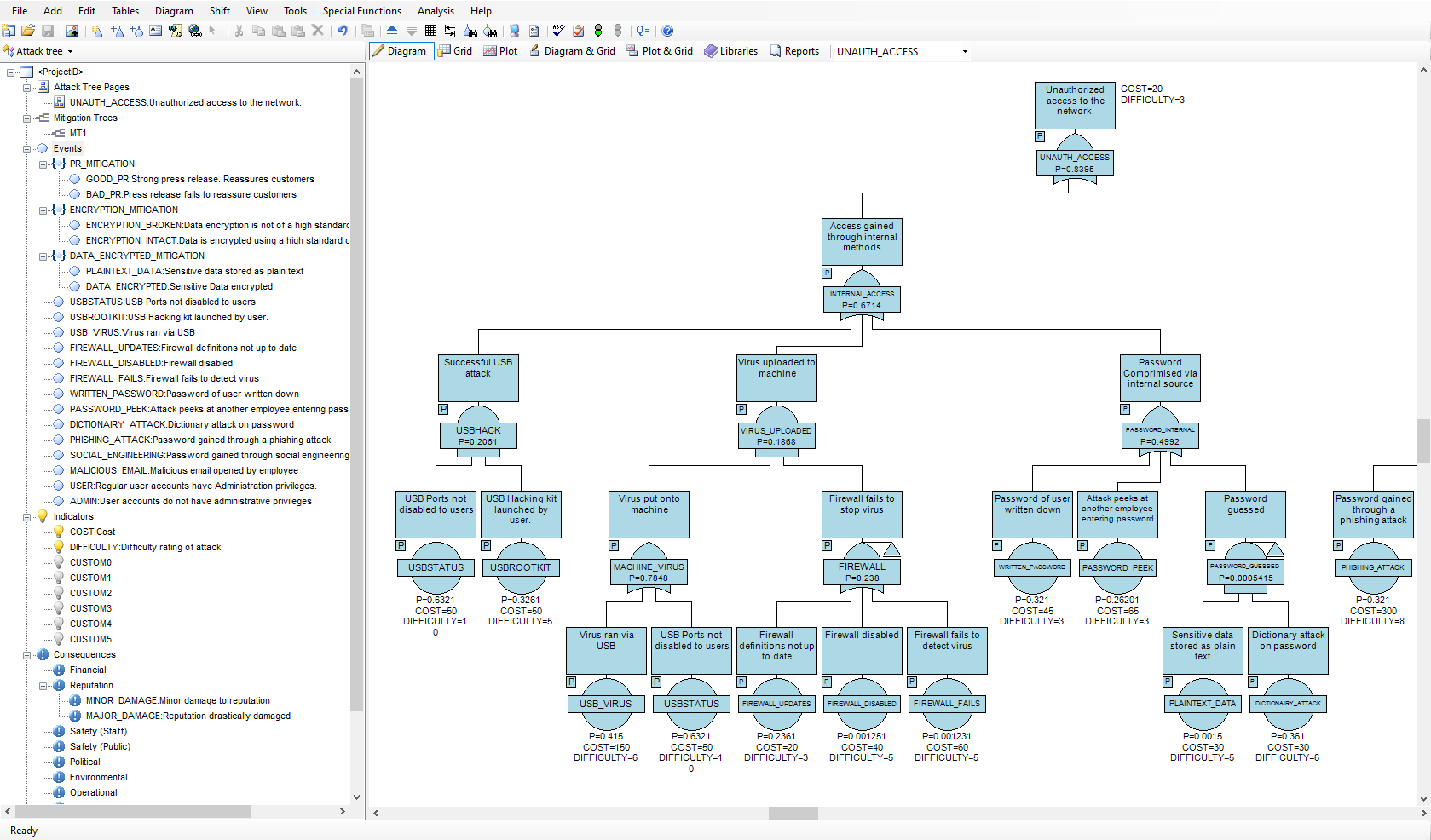
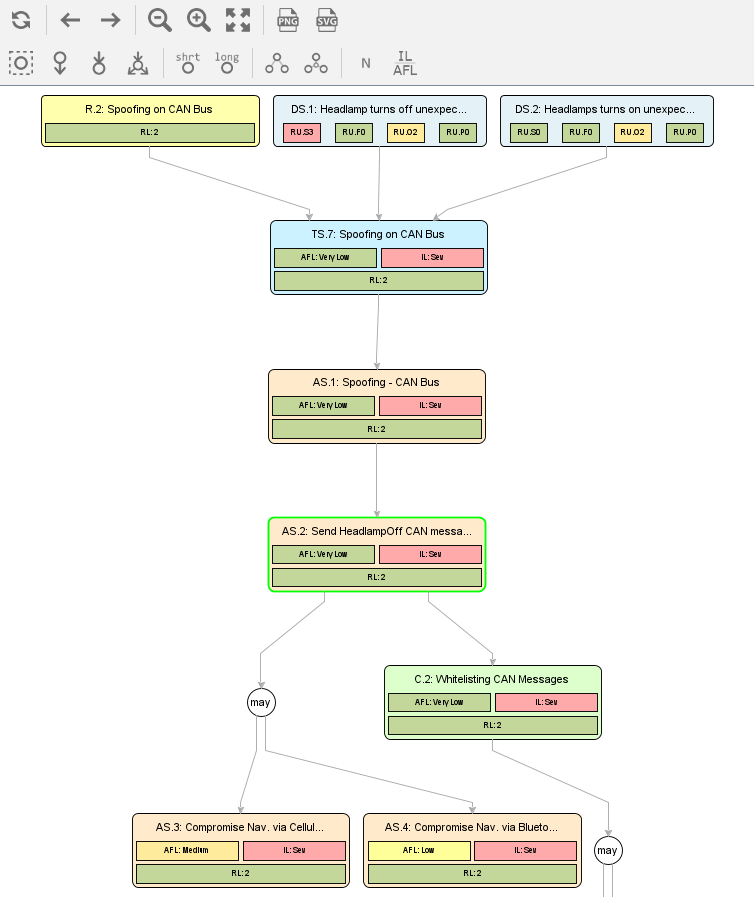
A valuation identified by the CSP-based tool for the attack tree in... | Download Scientific Diagram

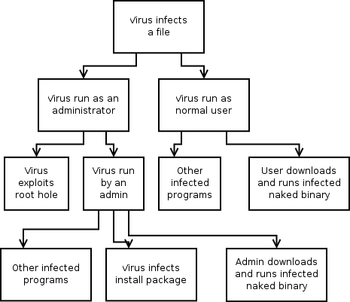
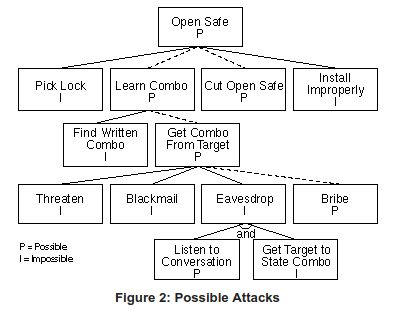
Section 1.3. An Alternative: Attack Trees :: Chapter 1. Threat Modeling and Risk Management :: Secure Linux-based Servers :: Linux systems :: eTutorials.org

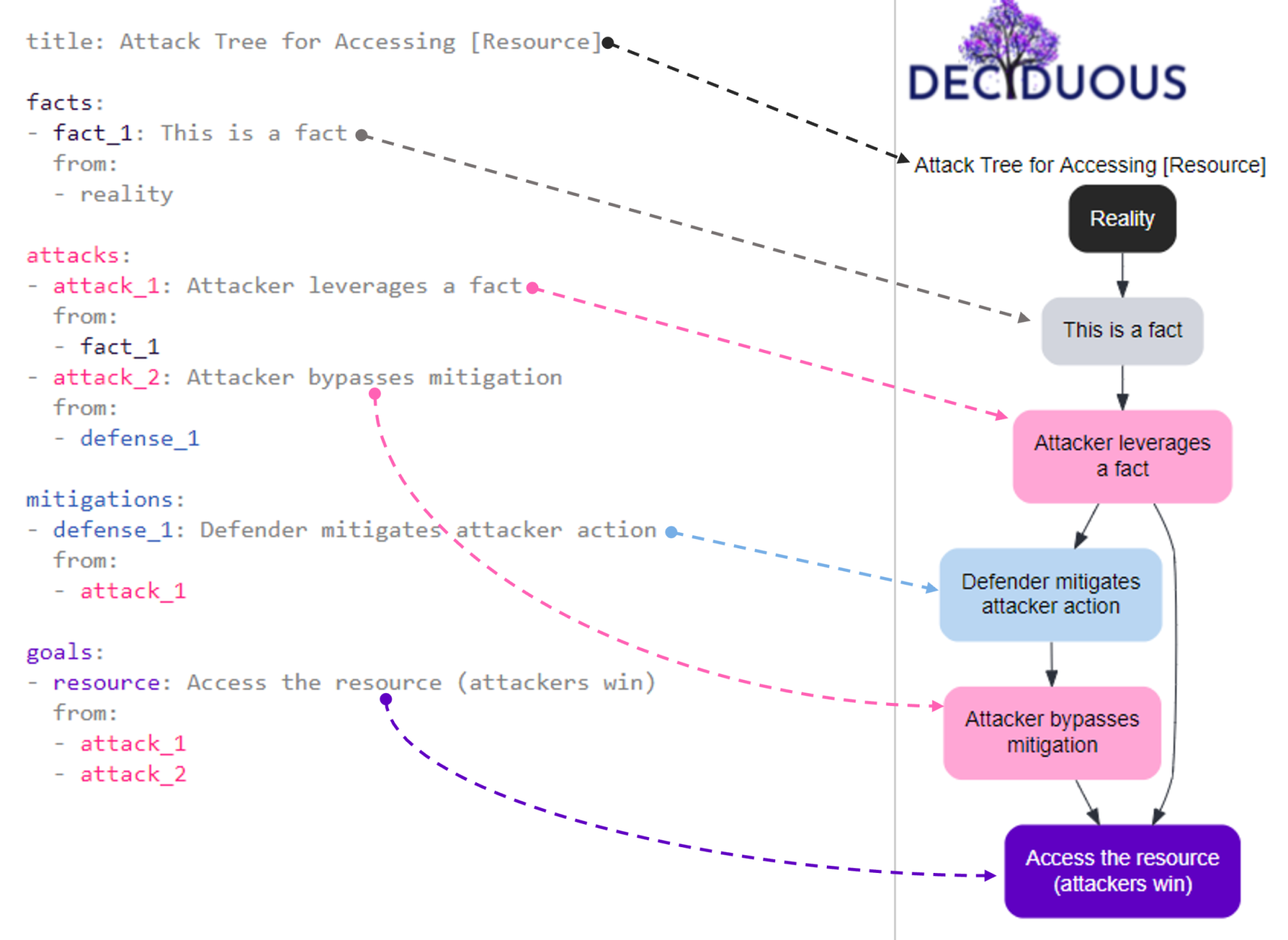







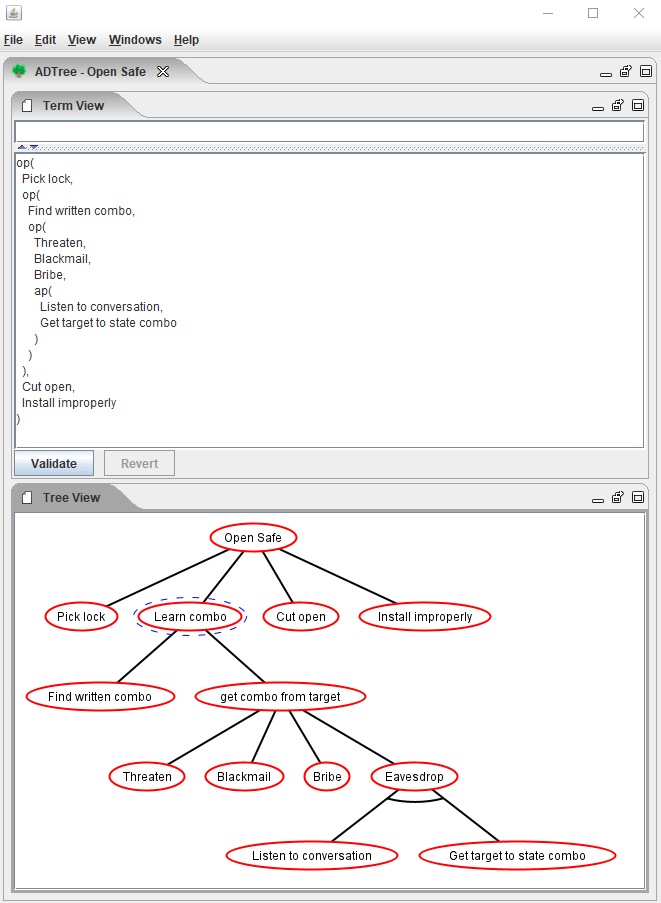
![PDF] On the Meaning and Purpose of Attack Trees | Semantic Scholar PDF] On the Meaning and Purpose of Attack Trees | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/aa9e791e982eec2b042f3f442b6f99e820863ae5/3-Figure1-1.png)