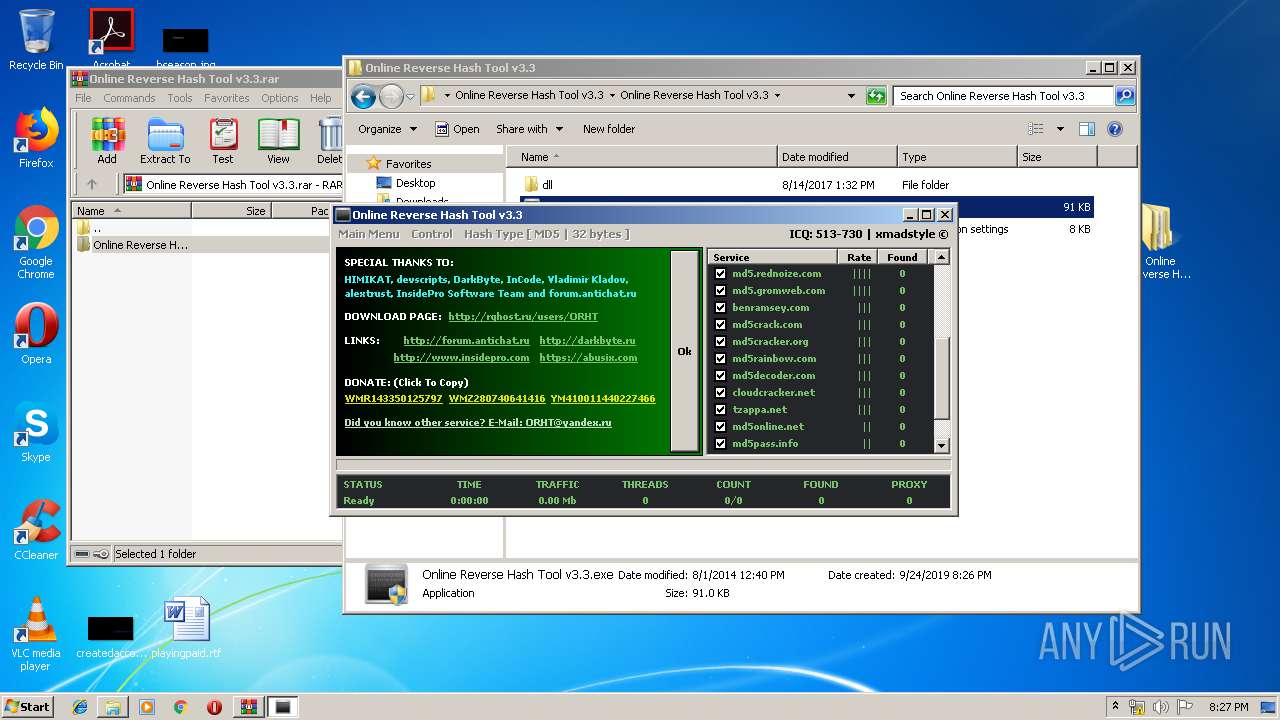
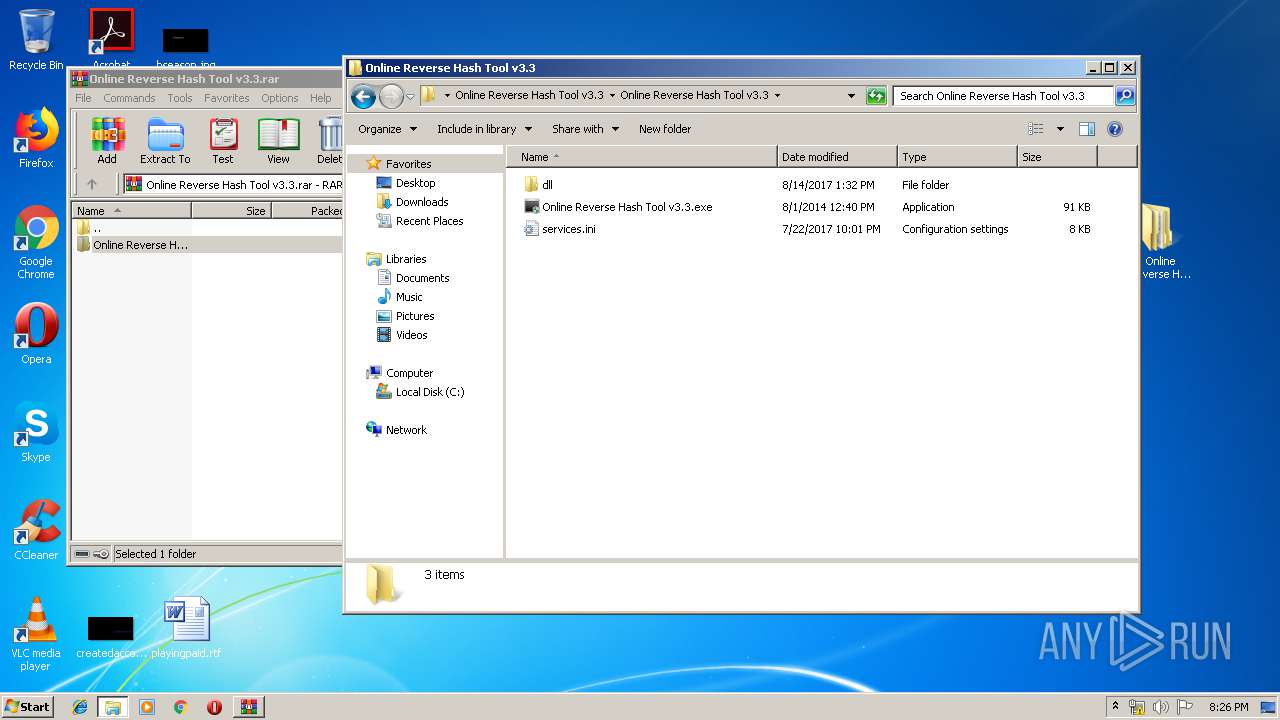
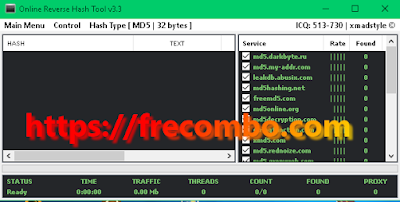
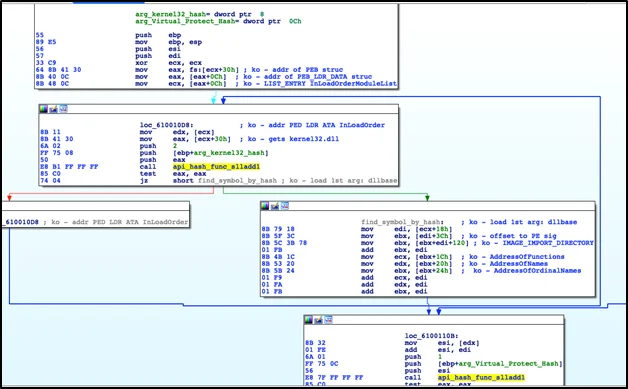
Malware analysis Online Reverse Hash Tool v3.3.rar No threats detected | ANY.RUN - Malware Sandbox Online

Free Automated Malware Analysis Service - powered by Falcon Sandbox - Viewing online file analysis results for 'Online Reverse Hash Tool v3.3.exe'

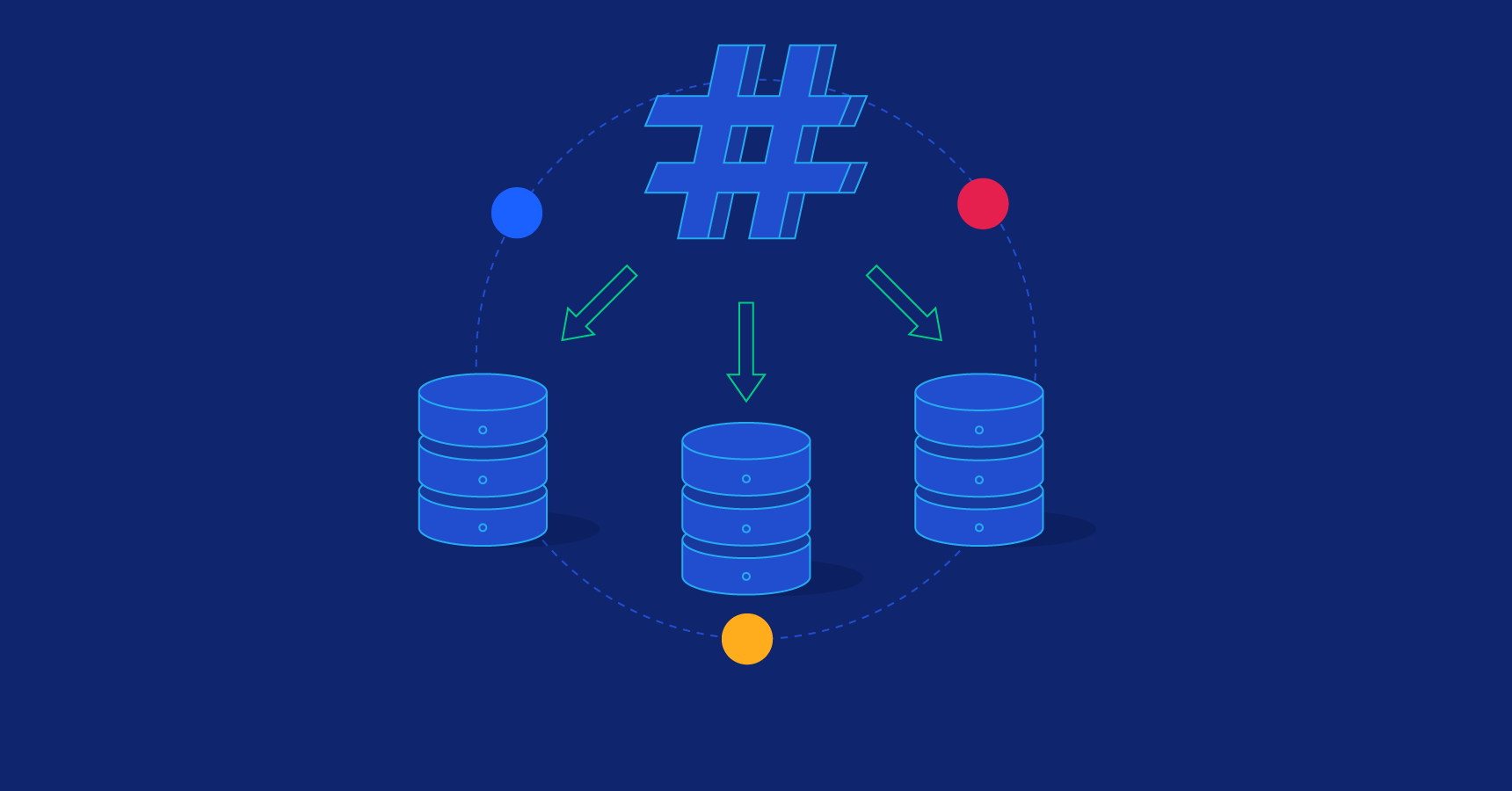
Simple, Fast, and Scalable Reverse Image Search Using Perceptual Hashes and DynamoDB - Canva Engineering Blog
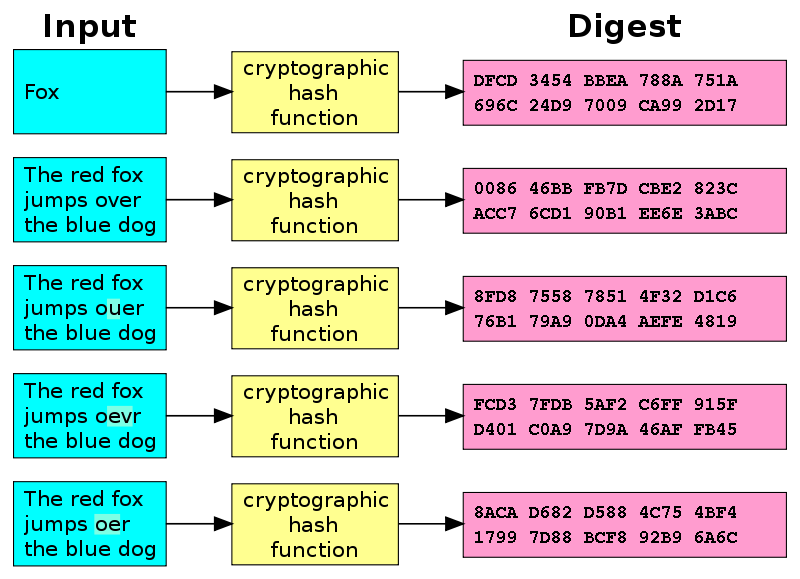
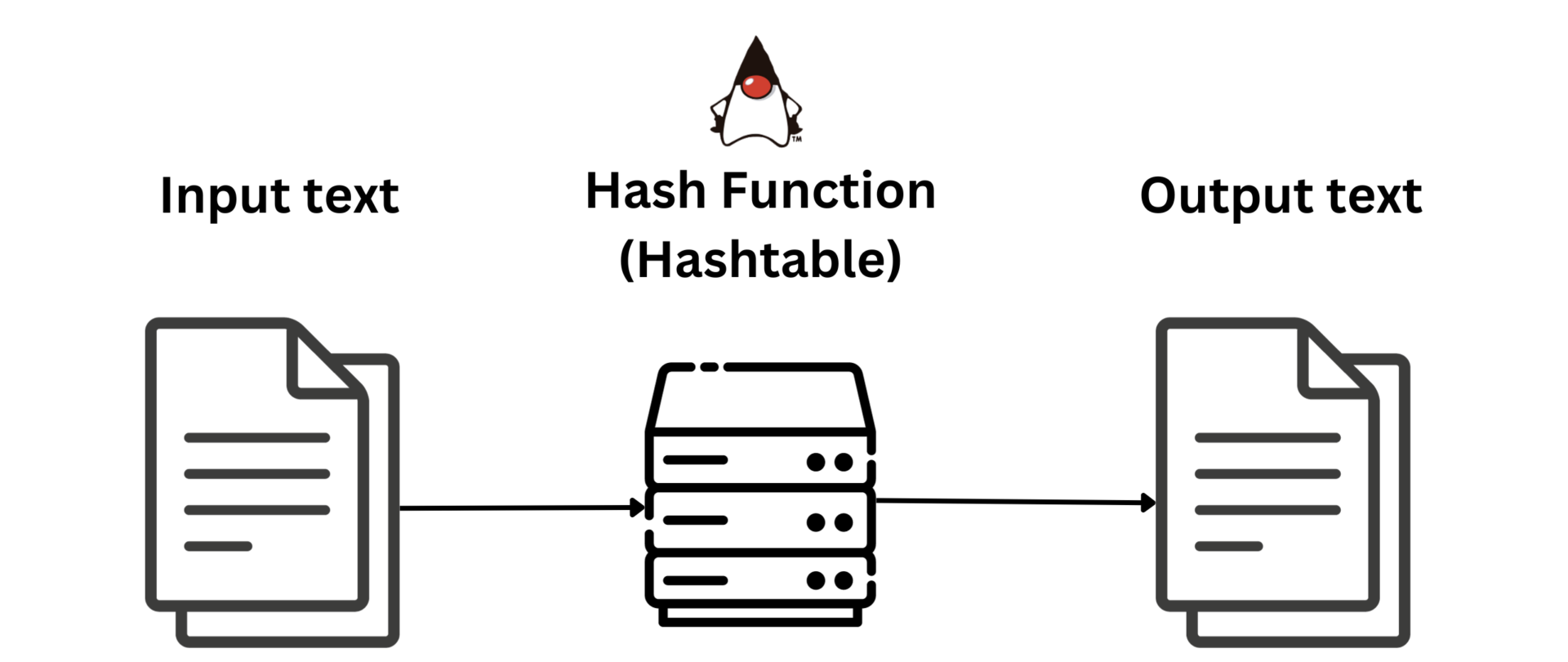
Identifying and Cracking Hashes. During a penetration test or a simple… | by Mr. Robot | InfoSec Adventures | Medium
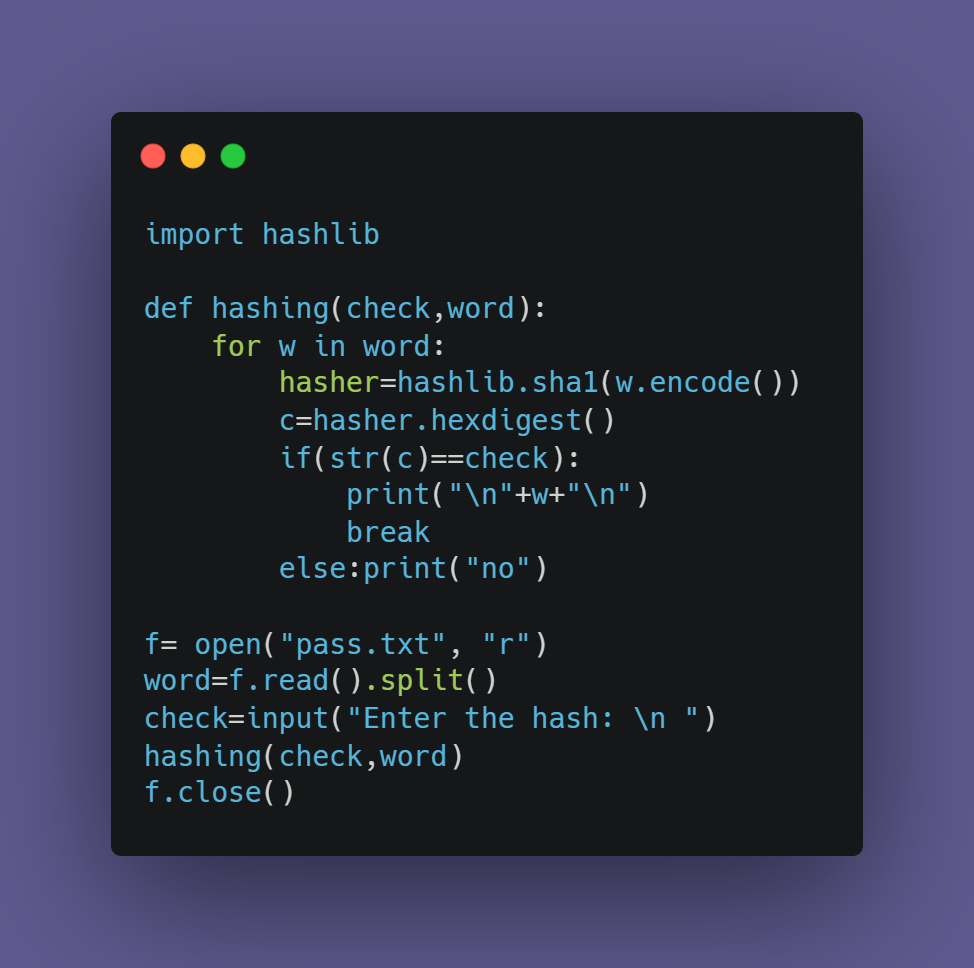
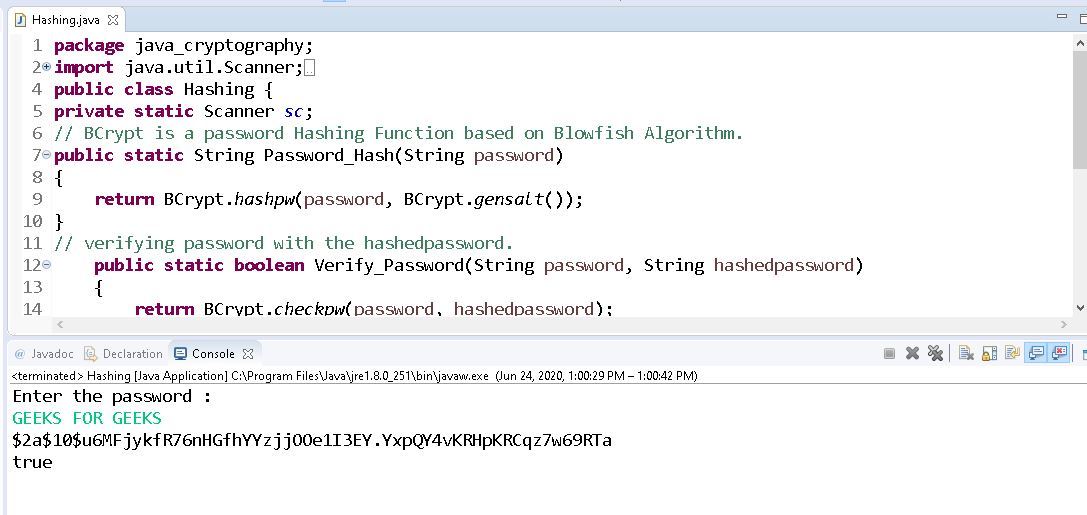
Breaking SHA-1 Hashes with Python: A Beginner's Guide to Hash Cracking | by Adithyakrishna V | Medium




:max_bytes(150000):strip_icc()/miracle-salad-md5-hash-generator-a6390b6d6fc3473bbd76526eb796975d.png)

![Online Reverse Hash Tool v3.4 [HASH COMBOS FIXER] - Cracking Tools - Nulled Online Reverse Hash Tool v3.4 [HASH COMBOS FIXER] - Cracking Tools - Nulled](https://i.imgur.com/ImgrF7b.png)